AI ETHICS IN NATIONAL SECURITY
by Tobin M. Albanese
Abstract. This piece proposes a practical assurance frame for deploying AI in national-security missions. It focuses on mission triage, accountability structures, provenance and audit, red-team practice, and incident response—emphasizing operational priors over lab-only metrics. The throughline is simple: reliability is a system property earned by process, proof, and humility, not a model statistic alone.

Executive Summary
- Mission-first fit: Only deploy where the cost of error is acceptable and understood.
- Clear ownership: A RACI-L matrix prevents ethical diffusion and ensures actionability.
- Assurance evidence: Decisions must be backed by test artifacts, logs, and red-team findings.
- Human authority: Define HITL/HOTL roles and keep a real kill-switch with pre-rehearsed rollback.
- Ongoing monitoring: Shift-aware evaluation and subgroup calibration are non-optional.

Context & Problem Framing
“High stakes” is not a vibe; it’s a measurable harm model. We map use cases by consequence (strategic, legal, human) and controllability (time to intervene, reversibility). Systems that front-run human judgment or route kinetic effects demand stronger guarantees than advisory analytics. This framing turns abstract ethics into concrete gates.
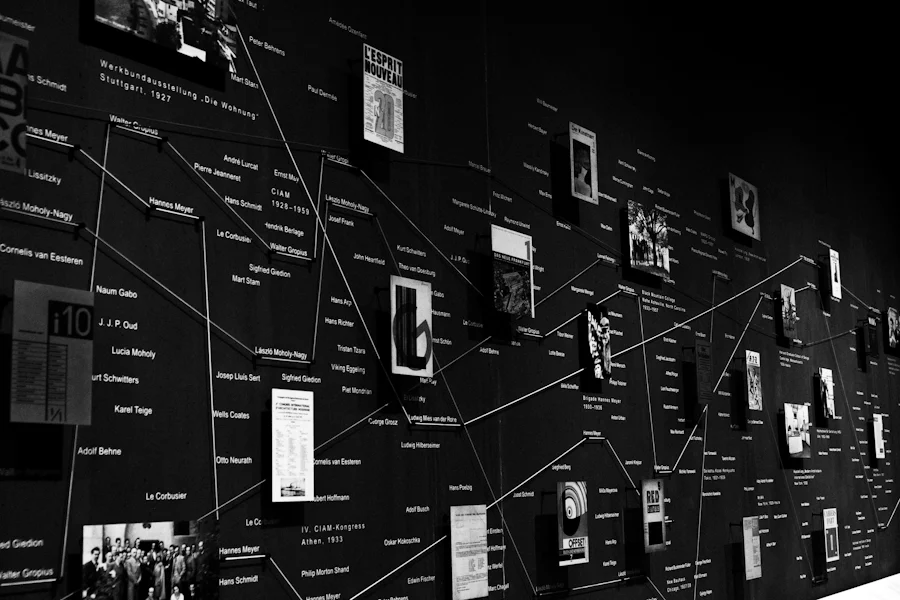
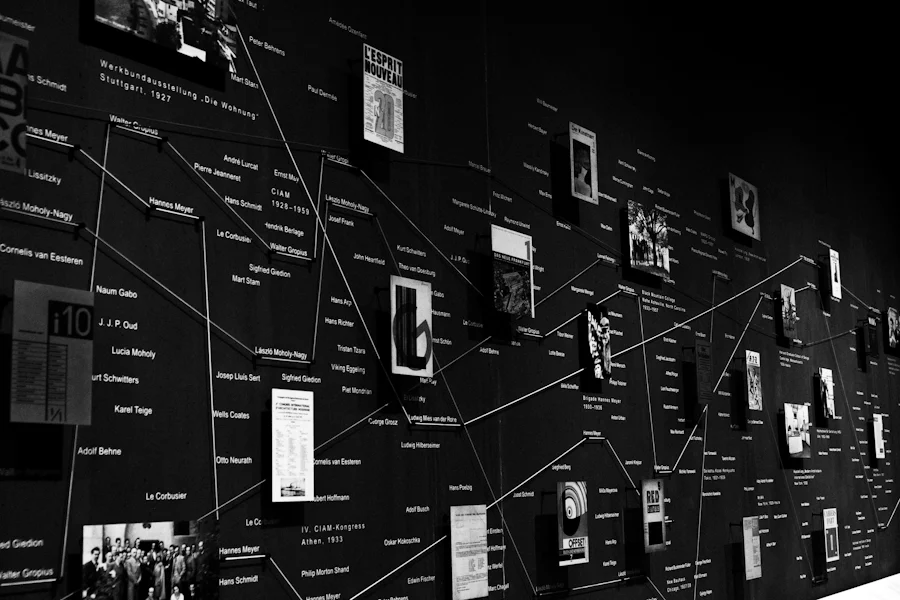
MARA: A Working Frame
- Mission: What decision is supported, who is affected, and what alternative exists without AI?
- Accountability: Who is responsible, who is accountable, who is consulted, who is informed—and what is logged?
- Risk: What are FP/FN harms at operational base rates? What are adversarial and abuse risks?
- Assurance: What evidence shows the system is fit for purpose under shift and stress?
Data Governance & Provenance
- Lineage manifests: dataset IDs, hashes, licenses, collection conditions, and exclusions.
- PII hygiene: minimization and masking; legal bases documented; retention with TTLs.
- Documentation: model cards + system cards describing human workflow and limits.
{
"dataset": "imagery_v5",
"hash": "sha256:…",
"license": "gov-owned",
"pii_controls": ["face_blur"],
"exclusions": ["schools", "hospitals"]
}
Development Lifecycle & Gates
- Sandbox: offline evals, ablations, threat modeling.
- Shadow mode: compare against human baseline; no operational impact.
- Limited release: time-boxed, narrow population, SLOs + rollback rehearsed.
- Operationalization: 24/7 on-call, dashboards, post-incident protocol, version pinning.
Evaluation Under Operational Priors
Confusion matrices are necessary; confusion costs are decisive. We weight FP/FN by mission harm and pick thresholds accordingly. We report reliability curves (calibration) per subgroup and use drift detectors to flag base-rate shifts. The goal is not a single AUC but a portfolio of stress results that survive contact with reality.
| Scenario | Shift | Mitigation | Owner |
|---|
| Night imagery | SNR drop | Threshold raise + HOTL | Ops lead |
| New sensor | Domain shift | Recalibrate + gate to shadow | Model lead |
| Adversarial spoof | Distribution spike | Rule-based block + IR | Sec engineer |
Red-Teaming & Safety Cases
- Threats: data poisoning, prompt/goal injection, sensor spoofing, targeted subgroup failure.
- Evidence: attach red-team reports to a safety case dossier with hazard analysis and residual risk acceptance signed by the accountable owner.
Runtime Controls & Logging
- Full decision trace (input → features → model/version → policy → human action).
- Override capture with rationale and authority level.
- Immutable, queryable logs supporting external audit.
{
"ts":"2025-02-10T03:12Z",
"model":"recce-v3.2",
"ver":"a1b2c3",
"score":0.91,
"threshold":0.95,
"action":"HITL escalate",
"override":true,
"by":"ops_412",
"reason":"low-illumination edge case"
}
Incident Response & Learning
- Declare severity; freeze model version; preserve evidence.
- Root-cause (people, process, tech); assign corrective actions.
- Update safety case; communicate to oversight; schedule follow-up eval.
Policy Notes & Open Questions
- Binding the kill-switch to a specific role with audit.
- How to write sunset clauses for models when mission context changes.
- Publishing red-team summaries without operational leakage.
Forthcoming ResearchGate preprint link will be added here.
Resources & Links
Government & Defense Guidance
Testing, Red-Team & Safety